Table Of Contents
Rubber Ducky is the “technical” name of a USB device which looks like a USB thumb drive, but presents itself to the computer as a USB keyboard, which, once plugged in, starts typing away pre-recorded keystrokes at super-human speeds. It can bypass many IT safeguards since the computer detects it as a keyboard, and it can easily fool people. Someone might think they’re just plugging in a harmless USB thumb drive, or even just a harmless iPhone charging cable. These can be disguised as just about anything these days, and they can be microscopic.


History-Making Attack
In 2010, the media covered the first time a real supply-chain cyber-weapon was used in the wild, Stuxnet. Stuxnet was a virus that infected the Natanz nuclear power plant in Iran. It used 20 zero-day vulnerabilities, making it one of the most advanced viruses ever created. The virus infected an air-gapped programming computer, and modified the payload after the compiler. It acted on program as it was uploading to the devices. Stuxnet changed the rotation speed of nuclear enrichment centrifuges, increasing pressure in critical points. The facility had sensors to account for this, but the virus changed those sensor values as well to remain undetected. By most accounts, the facility had good security, and we can’t really say that they didn’t know what they were doing. They however weren’t ready for the threat, because they weren’t aware of these attack vectors. But now about delivery.
Someone dropped a USB stick near employees in key positions, and one of them found it and had the brilliant idea of connecting it to his computer to see its contents. Once inside the computer, it could prep the computer for rest of the attack.
Why use a Ducky?
Laziness… and it educates people about existing risks they might not have been aware of yet. As any security conscious company does, we have policies about locking your computer when you walk away from your desk. But how do you make sure people really do it? Well in our case we decided that having fun at the expense of the offender is the most impactful. If someone walks away from their computer and leaves it unlocked, someone from the team just sits down at their computer and changes their background, maybe flips their screens, and so on, they are free to get creative. Once I replaced the busy cursor icon of my boss’ computer with a troll face, he always locks it now. People get creative, and from a security perspective, it builds great habits, but be careful with any risks you might accidentally add. Never download things off the internet to another person’s computer, and make sure to keep track of what you changed so it can be changed back.
USB Rubber Ducky as a Security Tool
The threat is more real than that, and education is the best defense in the world of cybersecurity. Cybersecurity is everyone’s job, and the more aware people are, the most secure everything is.
When I saw the rubber ducky for sale for $45 a few years ago, it was a must-have for many reasons. Changing people’s backgrounds and flipping screens is fun, but it can take a bunch of time. Also, creativity in the moment when the opportunity presents itself might just fall short of being really funny. As developers we like to automate any repetitive thing, and that’s where the ducky comes in. We can now just script everything, and maintain a central repository of scripts, and raise awareness of threats all at the same time. As a proof of concept, it’s obvious that it also reduces our work, by simply plugging in a usb drive to the unsuspecting locked computer policy violator. Better yet, leaving it around for them to find and plug in themselves. Unfortunately, this POC exercise was so effective, we can go months without a single opportunity, but we’re constantly hiring, and we might just expand the program to include other teams.
Setting up a Rubber Ducky
First, obviously you’ll need a ducky. The Hak5 store is a great place to pick one up https://shop.hak5.org/products/usb-rubber-ducky-deluxe
Once you have your ducky, take it apart, and you’ll see the USB chip, covers and a micro-usb card. Your program goes on the memory card. Plug the memory card into a card reader, so you can upload your program. If you plug the USB A, that’s the part that acts like a keyboard, and you might not want that.
Download the JS Ducky Encoder https://downloads.hak5.org/ducky and open jsencoder.html.
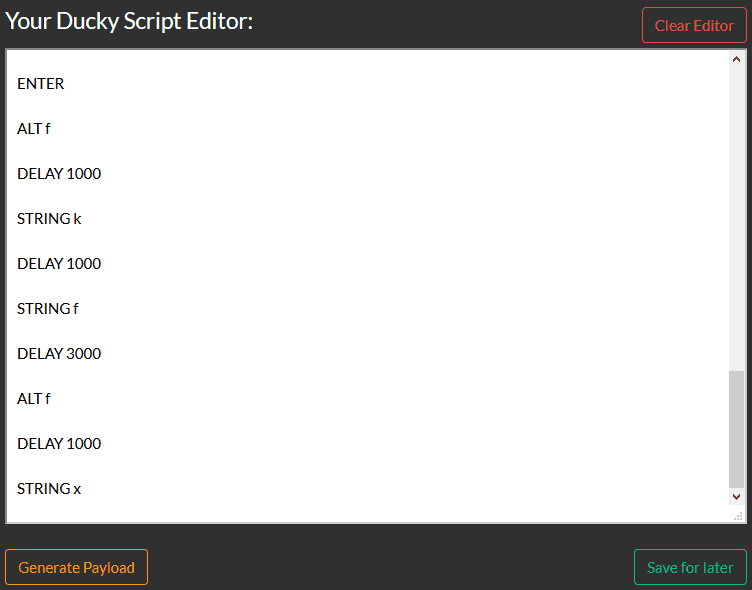
Add your script, in this case we’ll have the ducky use chrome to download a image, but you can just as well inline a powershell script. Then we’ll have chrome save the image, we’ll open mspaint, and click File -> Set as desktop background -> Fill.
REM ------------------------------------ REM :Credz Go To Kylerees64 REM :Some Help From KentosTheFreshmaker REM ------------------------------------ DELAY 500 GUI r DELAY 500 REM The Link Of Your IMG STRING chrome.exe http://www.thecuriosityworkshop.com/wp-content/uploads/2015/03/01-rubberduck-hongkong.jpg ENTER DELAY 1500 CTRL s DELAY 500 STRING %userprofile%\downloads\giantduck.jpg ENTER GUI r DELAY 500 STRING mspaint ENTER DELAY 150 CTRL o STRING %userprofile%\downloads\giantduck.jpg DELAY 100 DOWNARROW ENTER ALT f DELAY 1000 STRING k DELAY 1000 STRING f DELAY 3000 ALT f DELAY 1000 STRING x
Click Generate Payload
Upload the file to your micro usb card
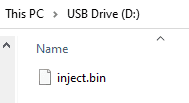
Now reassemble the ducky, and you’re ready to go.
https://github.com/hak5darren/USB-Rubber-Ducky/wiki/Change-the-background-to-MyLittlePony-(win10)
Why You Shouldn’t Do This
Of course you should never actually do this. Just think of how easy and funny it would be to a pen-tester or actual bad guy to just swap your own rubber ducky with his. I’d say use this as a tool to educate, and a great demo of just how effective an attack like this can be. But it’s one of those tools that has a great visual impact when people see it. Rubber duckys are also a great tool for you to test your security inhouse, and make sure your network is protected against this type of attack. I’ve seen several examples where USB data drives were disabled by Group Policy, and keyboards were still allowed. Best to be sure.
Other types of USB attacks
https://www.bleepingcomputer.com/news/security/heres-a-list-of-29-different-types-of-usb-attacks/
https://zh.iiixys.cc/blogs/news/stealing-files-with-the-usb-rubber-ducky-usb-exfiltration-explained
Related Posts
Subscribe To My Newsletter
Quick Links
Legal Stuff


